A couple of articles regarding cyber attacks in Australia.
This.
You don’t need multiple towers or triangulation or trilateration. You just need one tower that the phone associates with, and that one tower asks the phone where it is and the phone reports its GPS location to the tower (using GPS in its generic sense i.e. GNSS).
Reports of the use of a stingray suggest that - cell tower association was used to locate to within the catchment area of one tower, refined by sector and other RF techniques, and then a Stingray (fake cell tower) was used to interrogate the phone. *
I don’t know that Ms Maxwell was ‘hiding’ as such but clearly anyone who wants to ‘hide’ should drive to a remote location and leave the mobile phone there forever, before going to the ‘hiding’ place. Anyone who can afford to propose $37 million bail isn’t going to miss one mobile phone.
Mobile phones are tracking devices that just happen to be able to make phone calls.
* I have often wondered whether mobile phones can and should provide an alert, requiring confirmation, when a mobile phone tower just pops into existence out of nowhere. That would be no good if you are on the road but if you are at home, whether ‘hiding’ or not, new phone towers don’t come along very often. This has applications beyond dodgy Stingrays e.g. illegal repeaters or even legal repeaters.
I think concern about Chinese phones goes way beyond being able to track them even when they are “off”. That would seem to be the tip of the iceberg of possibilities.
PS I don’t know that you can actually turn the GPS receiver off - as long as the phone has power. Certainly with an Android phone / iPhone you have no way of knowing whether the GPS receiver is on or off.
GPS is turned off on my Android phones. It is just a setting. No point in chewing up battery for no reason, unless I need GPS on. Same with WiFi and Bluetooth and Data.
More likely the receiver is asleep or inactive. Also saving all that power needed to process the incoming data stream.
The switch is just a software driven function. How many different ways to send the appropriate bit/s to a fixed address in the phone, no one knows for sure. Supposedly secret Android or Apple code developers business.
P.S.
The power of what one can do remotely using the ‘Find MY Phone’ features suggests there are few limits.
Nah. I think you missed the point. Unless you are solid in circuit design, what does ‘off’ mean? See the link that was posted above: https://techpp.com/2013/08/22/track-phone-turned-off/
It’s the same with, for example, Bluetooth. I use Bluetooth specifically as an example because, on an iPhone, Bluetooth has three settings: on, off, really off. (OK, there might be a fourth setting that can only be achieved with @Fred123’s blocksplitter.)
Another doozey courtesy of the Qld Police.
Another massive data breach.
One small comment in a much bigger story … it isn’t a good idea to put your real birth date on social media.
Ok @person. Yes, I did miss the point. Is “off” really off when it is done in software, or indeed if there is power present.
Google has taken my birthday and applied US date format to it. I’m fine with that ![]() .
.
If all else fails:
Whilst waiting to be served at our local LPO a few days ago, I watched a person who I had not seen there before photocopying 2 x passports for a customer.
He checked each copy before stacking it on top of the others, but in the case of any that had not copied properly, he simply scrunched up and tossed in the bin.
I sincerely hope that they either shred the bin contents at closing time or sent them to a secure document destruction facility, or there would be a virtual treasure trove for identify theft.
Anything like photocopies or other paperwork no longer required, treated as “behind the counter” is sent for secure destruction. Even often times the front rubbish bins obtain the same treatment, but the risk is one in that case for the user to take into account that it may not be handled securely.
I certainly hope so as an Auspost rubbish bin would be an Aladdin’s Cave for identify thieves.
It’s a requirement of operation, part of their code of practice.
I just had a go at updating my password on one of the big 4 bank sites. Gobsmacked does not do justice…
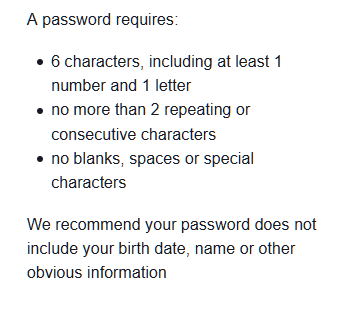
Yes, 6 characters, not 5 or 7 and the rest? For their high security protocols you cannot reuse the previous 3 passwords. Words escape.
So you are unable to use more than six characters? One has to hope that the bank has some sort of protection against brute force attacks, as six characters can be cracked in less than a second.
If the bank has protections against multiple guesses, then it is a little more secure. I wonder what the regulator would say about such flimsy protections. That said, it is unclear whether the complaint should be to APRA (systemic issue) or AFCA (individual dispute). My first guess would be APRA, as all customers of the bank would face the same flimsy security.
I could not deal with that bank, as my passwords are a minimum of 20 characters (including special characters).
When we operated internet kiosks using a very secure program which was then running on XP, we used an 18 digit alphanumeric password including upper case letters.
To my amazement, on one occassion only, someone managed to hack one kiosk and reboot it out of the secure mode so as to use it for free.

