I purchased a three-pack mesh network device which came with an extra node as a part of a promotion on Amazon for a very cheap $99. I returned it 11 days later due to privacy concerns and not working with my Foxtel box. I was happy with the ease of setup and the measured wifi speeds.
The first problem I found was my Foxtel box buffered streaming of programs every few seconds if I connected through this Tenda mesh wif but worked flawlessly when I connected directly to my wifi modem.
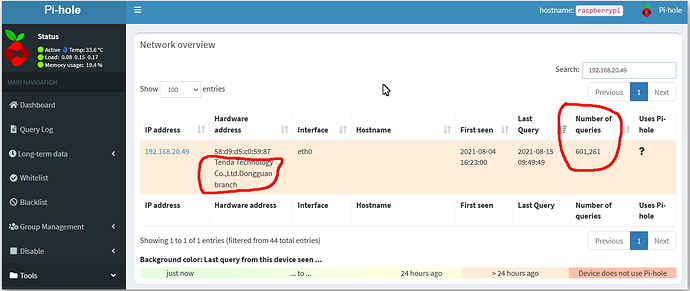
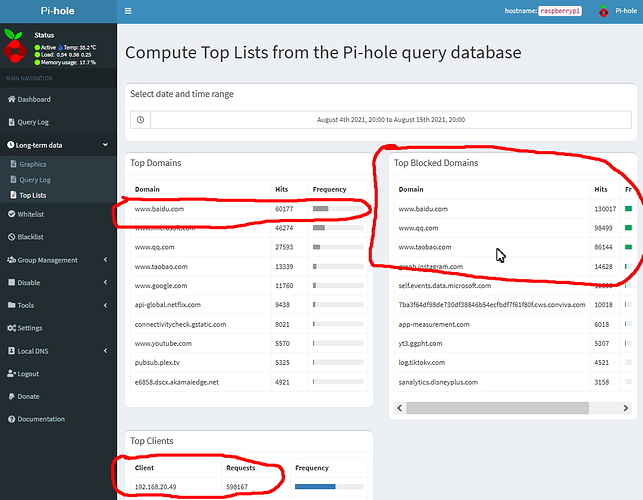
The next problem, and the most shocking, was that this Tenda mesh network device was contacting three websites thousands of times every single hour. My logs showed that the Tenda mesh wifi made over 600,000 individual queries over eleven days. I know of these 600k queries because I run a Pi-Hole system on my network which blocks internet advertising, and it logs all queries to the internet and from which devices the queries come. My Tenda mesh system was on my home network on 192.168.20.49.
I did a google search and found that the majority of the 600,000 queries were to these three Chinese websites.
www.bidu.com
www.qq.com
wwwtaobo.com
This was the device - Tenda Nova MW3 Whole Home Mesh WiFi System Pack of 3
Amazon link - https://www.amazon.com.au/gp/product/B07D9CC637/ref=ppx_yo_dt_b_asin_title_o06_s00?ie=UTF8&psc=1
Thanks for the warning.
That amount of unwanted traffic will kill your normal bandwidth expectations.
A device to avoid.
That would be concerning. The sites look like shopping and news. Can you advise what the queries were?
Did you contact Tenda to ask what their device is doing?
This activity could be interesting to network security agencies for multiple reasons, and if you still have logs of the internet transactions (or even if you do not) https://www.cyber.gov.au/ may be interested in your report.
@SteveDuncombe, maybe something you are interested following, including for future reviews?
What model was your system?
Have you considered contacting Australian tech review and magazine sites (eg Tech Advisor)? They seem to review Tenda mesh favourably. This may confirm and strengthen your findings if independent analysts come up with the same behaviour and do the public a good turn if these contacts are up to no good.
Thanks for reporting.
Three questions arise in my mind.
- Are the two problems related? That amount of spurious traffic would kill my internet connection and buffering would be inevitable.
- Were you blocking those DNS requests in PiHole or merely logging the requests but allowing them through?
- (I understand that you have returned the devices but) Does this relate to some setting? That is, did you by default agree to some spammy / anti-privacy condition but it could be disabled somewhere in settings?
Ironically, if the mesh device had even the most basic DNS caching (and with a decent TTL on the target DNS record), you probably wouldn’t have noticed anything in PiHole.
Indeed.
What was the exact nature of the DNS query? Vanilla A/AAAA? Something else?
DNS queries are one thing but what did it do, or would it have done, by way of communication with the destination host? HTTP? HTTPS? Something else?
Or was the DNS query itself the communication? (I expect that DNS can be used for telemetry or other exfiltration although that’s not something that I have looked into in detail i.e. the best way to achieve that.)
This was the device - Tenda Nova MW3 Whole Home Mesh WiFi System Pack of 3
Amazon link - https://www.amazon.com.au/gp/product/B07D9CC637/ref=ppx_yo_dt_b_asin_title_o06_s00?ie=UTF8&psc=1
I have uploaded the screen shots of the queries from my Pi-Hole dashboard screen.
Thanks for that, but without the messages to the web sites (eg a protocol sniffer log), not so helpful to understand what is going on other than it is curious.
As you are an X-customer who could engage in a more detailed Q&A than us as observers, it would be a good one for Tenda to explain. Their support email is support@tenda.cn
Note that there are some significant typos in the domains given in your original post.
Just putting it out there: if you block a domain and the client device contains rubbish code then the block may cause an infinite loop of requests. That is, if the domain had not been blocked then perhaps only one request would have been made.
In that situation the problem then is that this WiFi mesh device is not compatible with PiHole (or any equivalent product - so wouldn’t work for me either) … and it still leaves open the question as to why this device is looking up Chinese online shopping domains anyway.
I don’t use PiHole so I can’t tell off the top of my head which “block” option you are using. The kinds of block options that (I think) are available are:
- give NXDOMAIN error
- return the unspecified / any (0) IP address
- give a success response but an empty ‘answer’ section
- return an explicit IP address (which may or may not be a reachable IP address)
It is possible that a different block option would have given different results.
Which option are you using?
@grahroll no doubt has expertise to share.
As the domains were (apparently) blocked, there is nothing to sniff.
The domains were spamming and not blocked initially and I blocked them AFTER I noticed a large volume of traffic to those sites. They were doing it before and after they were blocked.
The Pi-hole became the DNS server and any sites identified as being advertising go in a black hole. The user can also add domains? to blacklist as well which is how they were blacklisted by me.
My only reason and motivation to post here is to alert people of a potential issue with a product. I start to wonder if I should now delete my post if I am going to get the third degree.
If interested here is the Pi-hole website for any questions - https://pi-hole.net/
@jeoffer, your post has had the primary use of alerting those on the Community to a problem with a device. You have the smarts to find out what the issue is with unwanted traffic generated by the device.
Many others may not and wonder why things are buffering and things are slow.
Thanks again for the heads-up.
Something from left field…have you checked you don’t have malware.
There is Baidu.com virus which tries to embed its advertising into browsers…and I suspect that the same may apply for the other two Chinese advertising websites (unfortunately my mandarin isn’t flash to be able to search Chinese websites online for information). If there is an infection, it may be trying to ping the Chinese servers for the purpose of content.
The malware could have come from a range of sources…including any apps/software used to run the Mesh or browser cookies. Assume you used the OEM software/driver site rather than downloading drivers from another site on the web.
@jeoffer, the community is definitely thankful that you have shared your information about this Tenda hardware and warned us about it.
There are community members who I think see the unwanted traffic as a problem to perhaps be solved, thus the number of questions. The intent is not to challenge what you did/how you tested the problem/how it might be solved, but probably more of an intellectual exercise that at the same time may help other people who own that Tenda hardware or others from the company.
Again, thank you for sharing your experience and for putting up with the questions. We do appreciate it.
Thanks mate 
Also, to gain some insight into why Tenda is doing this, whether it is malicious or opportunistic or stupid or erroneous or …
However as the hardware has been returned, we presumably can’t make any progress towards that goal.
Gosh - I wonder where the Tenda was made? Could it possibly be China?
Do you have corroborating evidence that this particular product is faulty or malicious? It would help to understand what is going on if there was other information.
I would call 600,000 queries in 11 days “faulty”. Not fit for purpose if it’s going to kill my internet connection.
What it is called right now is not the key factor though, which is that we only have one set of data from one machine.